网友您好, 请在下方输入框内输入要搜索的题目:
若集合A={0,1},B={0,2},C={4,3},这三个集合的笛卡尔积为R,则R的第2个元素为(23)元组。
A.1
B.2
C.3
D.4
解析:若集合A={0,1},B={0,2},C={4,3},则这三个集合的笛卡尔积R的每个分量必然是一个三元组,所以R的第2个元素必然为一个三元组。
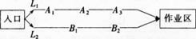
(1)求L1巷道中,三个易堵塞点最多有一个被堵塞的概率;
(2)若L2巷道中堵塞点个数为Χ,求Χ的分布列及数学期望EΧ,并按照“平均堵塞点少的巷道是较好的抢险路线“的标准,请你帮助救援队选择一条抢险路线,并说明理由。



RTK碎步点测量时,当测区面积较大,采用分区求坐标系统的转换参数时,相邻分区应不少于()个重合点。
A1个
B2个
C3个
D4个
B
全球定位系统实时动态测量(RTK)技术规范规定。
皮亚杰提出儿童认知发展的阶段有()。
A1个
B2个
C3个
D4个
D
略
1~2,1
1~2,2
2~3,2
3~4,3
苏教版初中数学八年级上册第一学期第20周周考试卷 一、选择题1传统佳节“春节”临近,剪纸民俗魅力四射,对称现象无处不在观察下面的四幅剪纸,其中是轴对称图形的有A1个 B2个 C3个 D4个()2如图,小手盖住的点的坐标可能为A(4,3)B(4,3)C(4,3)D(4,3)()3如图,在数轴上表示实数的点可能是() A点P B点Q C点M D点N4如图,已知ABC=DCB,下列所给条件不能证明ABCDCB的是() AA=D BAC=BD CACB=DBC DAB=DC5下列各组数为三角形的边长,其中能构成直角三角形的是()A, B3,4,5 C6,7,8D2,3,46关于一次函数y=x1,下列说法:图象与y轴的交点坐标是(0,1);y随x的增大而增大;图象经过第一、二、三象限; 直线y=x1可以看作由直线y=x向右平移1个单位得到其中正确的有 A1个 B2个 C3个 D4个 ()7在七年级的学习中,我们知道了|x|=小明同学突发奇想,画出了函数y=|x|的图象,你认为正确的是()AB CD二、填空题864的平方根是9点A(1,2)到y轴的距离是10一个等腰三角形的两边长分别为3和7,这个三角形的周长是11如图,OP平分MON,PAON于点A,点Q是射线OM上一个动点,若PA=3,则PQ的最小值为 12点(m,n)在直线y=3x2上,则代数式2n6m+1的值是13如图,ABC中,B、C的平分线交于O点,过O点作EFBC交AB、AC于E、FEF=6,BE=2,则CF=14如图,函数y=3x和y=kx+b的图象相交于点A(m,6),则关于x的不等式(k+3)x+b0的解集为三、解答题15(1)已知:(x+5)2=49,求x; (2)计算: +|1|+()216已知:y与x2成正比例,且x=3时,y=2(1)写出y与x之间的函数关系式; (2)当y4时,求x的取值范围17如图,已知点A、E、F、C在同一直线上,1=2,AE=CF,AD=CB判断BE和DF的位置关系,并说明理由18如图,直线y=2x+3与x轴相交于点A,与y轴相交于点B(1)求AOB的面积;(2)过B点作直线BP与x轴相交于P,ABP的面积是,求点P的坐标19在一次蜡烛燃烧试验中,甲、乙两根蜡烛燃烧时剩余部分的高度y(厘米)与燃烧时间x(小时)之间的关系如图所示,其中乙蜡烛燃烧时y与x之间的函数关系式是y=10x+25(1)甲蜡烛燃烧前的高度是厘米,乙蜡烛燃烧的时间是小时(2)求甲蜡烛燃烧时y与x之间的函数关系式(3)求出图中交点M的坐标,并说明点M的实际意义20在平面直角坐标系中,直线y=x+4交x轴,y轴分别于点A,点B,将AOB绕坐标原点逆时针旋转90得到COD,直线CD交直线AB于点E,如图1:(1)求:直线CD的函数关系式;(2)如图2,连接OE,过点O作OFOE交直线CD于点F,如图2,求证:OEF=45;求:点F的坐标;(3)若点P是直线DC上一点,点Q是x轴上一点(点Q不与点O重合),当DPQ和DOC全等时,直接写出点P的坐标
1个
2个
3个
4个
1个
2个
3个
4个
1个
2个
3个
4个
1个
2个
3个
4个
1个
2个
3个
4个
更多 “苏教版初中数学八年级上第一学期第20周周考试卷” 相关考题
- 下列属于"子病犯母"的病证是()A、水不涵木B、肝肾阴虚C、心肝火旺D、木火刑金E、肝郁脾虚
- 单选题Consider the Mysql Enterprise Audit plugin. Which statement is true when you identify a connection event that has used external authentication?()A The attribute STATUS is set to the string EXTERNAL_AUTHB The attribute PRIV_USER contains the usernameC The event type that is given in the attribute NAME is EXTERNAL_AUTHD There is no differentiation between native and external authentication eventsE External authentication is managed through external auditing logsF The PROXY_PRIV user shows a username if external authentication is used
- 多选题Which two statements are true about setting the per-thread buffers higher than required?()AMore memory per thread is beneficial in all scenariosBIt causes increased overhead due to initial memory allocationCIt can affect system stability during peak load times, due to swappingDIt requires increasing the thread_cache_size variable
- 多选题Which of the following are valid settings for the NLS_COMP parameter?()AASCIIBANSICBINARYDMONOLINGUALEMULTILINGUAL
- 多选题What are four capabilities of the mysql client program?()ACreating, dropping, and modifying tables and indexesBInitiating a binary backup of the database by using the START BACKUP commandCDisplaying replication status informationDShutting down the server by using the SHUTDOWN commandECreating and dropping databasesFCreating and administering users
- 单选题Evaluate the following block of code: BEGIN DBMS_NETWORK_ACL_ADMIN.CREATE_ACL ( acl = ’mycompany-com-permissions.xml’, principal = ’ACCT_MGR’, is_grant = TRUE, privilege = ’connect’); DBMS_NETWORK_ACL_ADMIN.ASSIGN_ACL ( acl = ’mycompany-com-permissions.xml’, host = ’*.mycompany.com’); END; What is the outcome of the above code?()A It produces an error because a fully qualified host name needs to be specified.B It produces an error because the range of ports associated with the hosts has not been specified.C It creates an access control list (ACL) with the user ACCT_MGR who gets the CONNECT and RESOLVE privileges.D It creates an access control list (ACL) with the user ACCT_MGR who gets the CONNECT privilege but not the RESOLVE privilege.
- 单选题Examine the following scenario: - Database is running in ARCHIVELOG mode. - Complete consistent backup is taken every Sunday. - On Tuesday the instance terminates abnormally because the disk on which control files are located gets corrupted - The disk having active online redo log files is also corrupted. - The hardware is repaired and the paths for online redo log files and control files are still valid. Which option would you use to perform the recovery of database till the point of failure?()A Restore the latest whole backup, perform complete recovery, and open the database normallyB Restore the latest whole backup, perform incomplete recovery, and open the database with the RESETLOGS option.C Restore the latest backups control file, perform complete recovery, and open the database with the RESETLOGS option.D Restore the latest backup control file, perform incomplete recovery using backup control file, and open the database with the RESETLOG option.
- 单选题An existing master-slave setup is currently using a delayed replication of one hour. The master has crashed and the slave must be "rolled forward" to provide all the latest data. The SHOW SLAVE STATUS indicates the following values: RELAY_LOG_FILE =hostname-relay-bin.00004 RELAY_LOG_POS = 1383 Which command set would make the slave current?()A Gtid_mode must be set to AUTO during point in time recoveriesB Mysqlbinlog ignores arguments to – exclude-gtids-it means ignore all events with GTIDsC The server keeps track of which GTIDs have already been executed and skips thoseD Enforce_gtid_consistency is set to ON
- 单选题You have created a script in the recovery catalog called backup_database. Which of the following commands would successfully execute that script?()A run { open script backup_database; run script backup_database }B run { engage script backup_database; }C run { run script backup_database; }D Run { execute script backup_database; }E The name backup_database is an invalid name for an RMAN script. Trying to run it from RMAN would result in an error.
- 单选题Consider the following: Which statement best describes the meaning of the value for the key_len column?()A It shows the total size of the index rowB It shows how many columns in the index are examinedC It shows the number of characters indexed in the keyD It shows how many bytes will be used from each index row